Snort is a lightweight, open source network intrusion prevention system for running a network intrusion detection system (NIDS). Snort is used to monitor the packet data sent / received over a specific network interface. Network intrusion detection systems can intercept threats that target your system weaknesses and vulnerabilities by using signature-based detection and log analysis technologies.
When properly installed and configured, NIDS software can detect various types of attacks and suspicions such as CGI attacks, network policy violations, SMB scans, malware infections, a compromised system, stealth port scans, etc.
In this tutorial we will learn how to install Snort 3 on Ubuntu 20.04.
Some of the new Snort 3 features:
- Supports multiple packet processing threads
- Allows multiple packets to be processed
- Generate reference documentation automatically
- Use a simple scriptable configuration
- Make key components pluggable
- Allows users to write their own plugins
- Common configuration and attribute table
- Allows rules to run faster
Step 1: update the system
Update and upgrade your Ubuntu system first
sudo apt update sudo apt upgrade
Step 2: Install required dependencies
The Ubuntu standard repository contains the Snort package. The Snort package available there is the old version. To install Snort 3 we need to build from the source. Before installing Snort 3, we need to install the required and required libraries.
Install Snort 3 dependency packages with the following command:
sudo apt install build-essential libpcap-dev libpcre3-dev libnet1-dev zlib1g-dev luajit hwloc libdnet-dev libdumbnet-dev bison flex liblzma-dev openssl libssl-dev pkg-config libhwloc-dev cmake cpputest libsqlite3-dev uuid-dev libcmocka-dev libnetfilter-queue-dev libmnl-dev autotools-dev libluajit-5.1-dev libunwind-dev
After the dependencies are installed, use the following command to create a directory where you will compile and keep source files for Snort:
mkdir snort-source-files cd snort-source-files
Then download and install the latest version of the Snort Data Acquisition Library (LibDAQ). To install LibDAQ we need to build and install it from source using the command below.
git clone https://github.com/snort3/libdaq.git cd libdaq ./bootstrap ./configure make make install
The next dependency is Tcmalloc, which optimizes memory allocation and provides better memory utilization.
Install Tcmalloc with the following command.
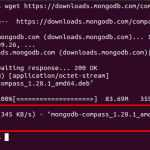
cd ../ wget https://github.com/gperftools/gperftools/releases/download/gperftools-2.9/gperftools-2.9.tar.gz tar xzf gperftools-2.9.tar.gz cd gperftools-2.9/ ./configure make make install
Step 3: Install Snort 3 on Ubuntu 20.04
After the dependencies are set up, we will download and install Snort 3 on Ubuntu 20.04.
01. Clone Snort 3’s official GitHub repository.
cd ../ git clone git://github.com/snortadmin/snort3.git
02. Change the directory to Snort3
cd snort3/
03. From there, configure and activate tcmalloc with the following command.
./configure_cmake.sh --prefix=/usr/local --enable-tcmalloc
04. Navigate to the build directory and compile and install Snort 3 with make and make install with the following command.
cd build make make install
05. When the installation is complete, update shared libraries.
sudo ldconfig
By default, Snort is installed in the / usr / local / bin / snort directory. It is recommended that you create a symbolic link for / usr / sbin / snort
sudo ln -s /usr/local/bin/snort /usr/sbin/snort
06. Check the installation of Snort 3
snort -V
Output:
,,_ -> Snort++ <-
o" )~ Version 3.1.10.0
'''' By Martin Roesch & The Snort Team
http://snort.org/contact#team
Copyright (C) 2014-2021 Cisco and/or its affiliates. All rights reserved.
Copyright (C) 1998-2013 Sourcefire, Inc., et al.
Using DAQ version 3.0.4
Using LuaJIT version 2.1.0-beta3
Using OpenSSL 1.1.1f 31 Mar 2020
Using libpcap version 1.9.1 (with TPACKET_V3)
Using PCRE version 8.39 2016-06-14
Using ZLIB version 1.2.11
Using LZMA version 5.2.4If you see similar output, then Snort 3 has been installed successfully.
Configuring network interface cards
Find the interface on which Snort is listening for network traffic and enable Promiscuous Mode to see all network traffic sent to it.
ip link set dev eh0 promisc on
Check with the following command.
ip add sh eth0
Output:
2: eth0: <BROADCAST,MULTICAST,PROMISC,UP,LOWER UP> mtu 1500 qdisc mq state UP group default qlen 1000
link/ether f2:3c:92:ed:7e:d8 brd ff:ff:ff:ff:ff:ff
inet 74.207.230.186/24 brd 74.207.230.255 scope global dynamic eth0
valid_lft 72073sec preferred_lft 72073sec
inet6 2600:3c02::f03c:92ff:feed:7ed8/64 scope global dynamic mngtmpaddr noprefixroute
valid_lft 60sec preferred_lft 20sec
inet6 fe80::f03c:92ff:feed:7ed8/64 scope link
valid_lft forever preferred_lft foreverNext, disable interface offloading to prevent Snort from truncating 3 large packets, 1518 bytes or less. Use the following command to verify that this feature is enabled.
ethtool -k eth0 | grep receive-offload
When this output is displayed, GRO is enabled while LRO is fixed or LRO is enabled.
Output.
generic-receive-offload: on large-receive-offload: on
Disable it with the command below.
ethtool -K eth0 gro off lro off
To ensure that the changes persist during the system reboot, we need to create and activate a systemd service unit to implement the changes.
sudo nano /etc/systemd/system/snort3-nic.service
Paste the following configuration pointing to your network interface.
[Unit] Description=Set Snort 3 NIC in promiscuous mode and Disable GRO, LRO on boot After=network.target [Service] Type=oneshot ExecStart=/usr/sbin/ip link set dev eth0 promisc on ExecStart=/usr/sbin/ethtool -K eth0 gro off lro off TimeoutStartSec=0 RemainAfterExit=yes [Install] WantedBy=default.target
Reload systemd configuration settings:
sudo systemctl daemon-reload
Start and enable the service at boot with the following command:
sudo systemctl enable --now snort3-nic.service
Output.
Created symlink /etc/systemd/system/default.target.wants/snort3-nic.service → /etc/systemd/system/snort3-nic.service.
Verify the snort3-nic.service with:
sudo systemctl status snort3-nic.service
Output.
● snort3-nic.service - Set Snort 3 NIC in promiscuous mode and Disable GRO, LRO on boot
Loaded: loaded (/etc/systemd/system/snort3-nic.service; enabled; vendor preset: enabled)
Active: active (exited) since Sat 2021-09-18 12:35:17 UTC; 4min 59s ago
Process: 182782 ExecStart=/usr/sbin/ip link set dev eth0 promisc on (code=exited, status=0>
Process: 182783 ExecStart=/usr/sbin/ethtool -K eth0 gro off lro off (code=exited, status=0>
Main PID: 182783 (code=exited, status=0/SUCCESS)
Sep 18 12:35:17 li72-186 systemd[1]: Starting Set Snort 3 NIC in promiscuous mode and Disable >
Sep 18 12:35:17 li72-186 systemd[1]: Finished Set Snort 3 NIC in promiscuous mode and Disable >Install the Snort 3 Community Rule Sets
In Snort, rule sets are the main benefit of the intrusion detection engine. There are three types of Snort Rules: Community Rules, Registered Rules, and Subscriber Rules. Community rules are submitted by the open source community or by Snort integrators.
We’ll show you how to install the community rules.
First create a directory for the rules in / usr / local / etc / snort
mkdir /usr/local/etc/rules
Download the Snort 3 Community Rules. You can find it on the official Snort3 download page.
wget https://www.snort.org/downloads/community/snort3-community-rules.tar.gz
Extract downloaded rules and place them in the / usr / local / etc / rules / directory created earlier
tar xzf snort3-community-rules.tar.gz -C /usr/local/etc/rules/
Snort 3 includes two main configuration files, snort_defaults.lua and snort.lua.
The snort.lua file contains the main configuration of Snort, which enables the implementation and configuration of Snort preprocessors, the inclusion of rule files, logging, event filters, output and so on.
The snort_defaults.lua files contain default values such as paths to rules, AppID, intelligence lists and network variables.
When rules files are extracted and placed, we configure one of these configuration files called snort.lua. Open the file with your favorite editor and you will see a similar configuration.
... -- HOME_NET and EXTERNAL_NET must be set now -- setup the network addresses you are protecting HOME_NET = 'server_public_IP/32' -- set up the external network addresses. -- (leave as "any" in most situations) EXTERNAL_NET = 'any' EXTERNAL_NET = '!$HOME_NET' ...
Set the value for the HOME_NET variable to the network that you want to protect against attacks and point the EXTERNAL_NET variable to the HOME_NET variable.
Save and close.
You can also edit the default Snort settings in /usr/local/etc/snort/snort_defaults.lua and define the location for your rules in the IPS section.
ips =
{
-- use this to enable decoder and inspector alerts
--enable_builtin_rules = true,
-- use include for rules files; be sure to set your path
-- note that rules files can include other rules files
include="/usr/local/etc/rules/snort3-community-rules/snort3-community.rules"
}
...Save and close.
Run Snort as a service
If you want to run Snort as a service daemon in the background, you can also create a systemd service unit for Snort. It is advisable to run it as a non-privileged system user
Create a system user account without logging in.
sudo useradd -r -s /usr/sbin/nologin -M -c SNORT_IDS snort
Then create a systemd service unit to have Snort run as a Snort user. Customize and customize your network interface.
sudo nano /etc/systemd/system/snort3.service
Paste the following configuration.
[Unit] Description=Snort 3 NIDS Daemon After=syslog.target network.target [Service] Type=simple ExecStart=/usr/local/bin/snort -c /usr/local/etc/snort/snort.lua -s 65535 -k none -l /var/log/snort -D -i eht0 -m 0x1b -u snort -g snort [Install] WantedBy=multi-user.target
Reload the systemd configuration.
sudo systemctl daemon-reload
Set ownership and permissions on the log file.
sudo chmod -R 5775 /var/log/snort sudo chown -R snort:snort /var/log/snort
Launch and enable Snort to run at system startup:
sudo systemctl enable --now snort3
Check the service status to confirm that it is running.
sudo systemctl status snort3
Output.
● snort3.service - Snort 3 NIDS Daemon
Loaded: loaded (/etc/systemd/system/snort3.service; enabled; vendor preset: enabled)
Active: active (running) since Sat 2021-09-18 12:44:32 UTC; 6s ago
Main PID: 182886 (snort)
Tasks: 2 (limit: 1071)
Memory: 62.6M
CGroup: /system.slice/snort3.service
└─182886 /usr/local/bin/snort -c /usr/local/etc/snort/snort.lua -s 65535 -k none >
Sep 18 12:44:32 li72-186 systemd[1]: Started Snort 3 NIDS Daemon.diploma
This tutorial will show you how to install the Snort 3 Network Intrusion Detection System on Ubuntu 20.04.
Linux is not 100% immune to viruses and suspicious things. It is always better to have a tool installed and to make sure that no one is attempting anything suspicious on your device and network. Other alternatives for Snort you can investigate: Ossec, Palo Alto Networks Next-Generation Firewall, Next-Generation Intrusion Prevention System (NGIPS).
Thanks for reading, please leave your feedback and suggestions in the comment section.
Discover more from Ubuntu-Server.com
Subscribe to get the latest posts sent to your email.